Nessus Vulnerability Scan
Lab Overview: Understanding Vulnerability Assessments with Nessus
Numerous vulnerability scanners are available, with Nessus being a widely utilized tool designed to assist organizations in identifying and resolving potential security issues within their systems.
To facilitate a practical understanding of vulnerability assessments, a comprehensive project guide has been assembled. Credit goes to Josh Madakor for inspiring this endeavor.
Requirements:
- VMware Workstation
- Windows 10 ISO file
- Nessus Essentials (accessible through a web browser)
Rest assured, all tools required for this lab are freely available.
Project Outline:
This project involves using Nessus Essentials to conduct vulnerability assessments on a virtual Windows 10 machine within VMware Workstation. The tasks include executing a regular scan, a credentialed scan, and testing the vulnerability of an outdated version of Google Chrome. By project completion, participants will have gained proficiency in utilizing Nessus Essentials for vulnerability identification, contributing to a secure network.
Initial setup details for VMware, Windows VM, and Nessus on the host machine won’t be provided, as these are standard procedures easily found in online resources.
Project Tasks:
Task 1: Run a Standard Scan on the Windows 10 VM
- Power on the Windows VM in VMware Workstation, ensuring it is on a “bridged network” for host communication.
- Confirm successful pinging from host terminal to the Windows VM.
- Launch Nessus Essentials via the host machine’s browser and create a new scan at https://localhost:8834/.
- Click “New Scan” and select “Basic Network Scan.”
- Specify the target IP (Windows 10 VM), name the scan (“Regular Scan”), and click “save.”

- Confirm settings and launch the scan.

- Monitor real-time progress, view results after completion.

Task 2: Execute a Credentialed Scan
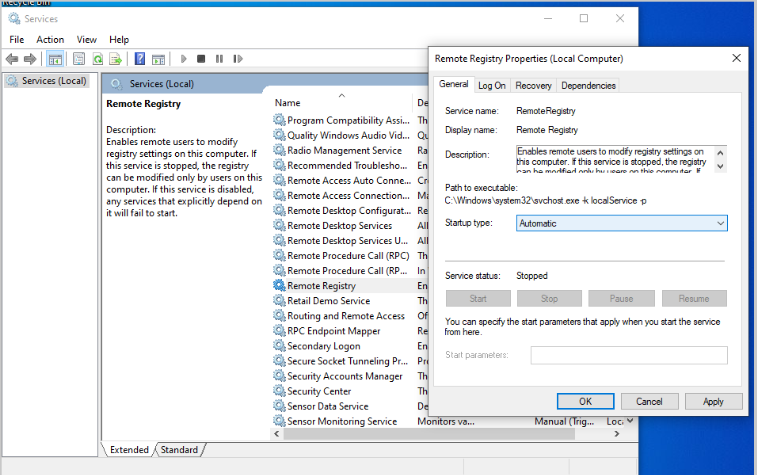
- Configure the Windows VM for a credentialed scan (enable remote registry, file sharing, adjust user account control, and add a remote key in registry editor).
- Launch Nessus Essentials, create a new scan (“Credentialed Scan”), and input credentials under the “Credentials” tab.
- Save settings, launch the scan (note: this scan takes longer).

- View results post-scan.

Task 3: Download and Scan an Older Browser Version
- Download an older Chrome or Firefox version from a reliable source and install.
- Relaunch Nessus Essentials, rerun the credentialed scan, and analyze results.


Task 4: Remediate Vulnerabilities and Conduct Another Scan
- Update Google Chrome to the latest version.
- Run Windows Update for additional vulnerability fixes.

- Re-launch the previous “Credentialed Scan” in Nessus Essentials.
- Analyze results.

Only one critical and high vulnerability remain post-update.
Project Insights:
This project provided hands-on experience using Nessus Essentials for vulnerability assessments. Participants learned to configure and run both regular and credentialed scans, understand the significance of updating software, and interpret and act on scan results to enhance system security.
Skills and Lessons Acquired:
- Grasped the importance of vulnerability assessments in maintaining network security.
- Familiarity with Nessus Essentials and its capabilities.
- Proficiency in configuring and executing regular and credentialed scans.
- Awareness of vulnerabilities in older software versions and the significance of updates.
- Interpretation and utilization of scan results for system security improvement.
Next Steps: Building on the Project
Completing this Nessus vulnerability scanning lab opens avenues for skill and knowledge enhancement in network security. Suggested next steps include:
- Implement Remediation Plans: Develop and execute plans to address identified vulnerabilities.
- Customize Scan Settings: Explore Nessus’ customizable scan settings for targeted vulnerability assessments.
- Perform Regular Scans: Establish a routine for regular Nessus scans to uphold network security.
- Further Research: Delve into more details about Nessus and other vulnerability scanning tools to deepen knowledge.
By incorporating these steps, participants can fortify their skills gained in this project, contributing to improved network security.

